How counterfeiting can be solved with the AI monitored serialization technology
Initial Draft: 08/16/2017
Revisions: 03/09/2018, 12/12/2018
Latest Revision: 02/16/2019
around $1.6 trillion as of today (Dec, 2018). There are a handful of partial solutions available, but none is really solving the core problem.
The solution to address the largest segment of merchandise counterfeited (ranging from $20 to $1000) need to be foolproof, and cost effective. The typical solutions offered today are holograms, rfid based tags, random 2D graph, scratchable QR codes, and Digital number based SMS system.
We found that every partial solution offered today to address counterfeiting can be counterfeited, meaning the tags or the scheme they employ can be copied and replicated easily. Below are our findings and rough estimate on how much it costs a counterfeiter to replicate and fool the solution provided.
Let’s explore each solution one by one:

All it takes to copy the hologram is, give one of the original to any hologram printer company and it will give you exact copies of it. It will even cost less to the Counterfeiters to get the exact Tags/Labels/Stickers from any hologram printing lab near them. Usually, the price ranges from less than 1¢ to 10¢ depending on the quantity, complexity, colors, layers, materials, and size involved.

Some companies claim they generate or print certain shape or graphs on the label whose photo can be taken and sent to the cloud servers to authenticate. Unfortunately, they are still the same, no matter what the company claims about running a Machine Learning or AI to scan the image on the cloud. The truth is anyone who can take photos of the sticker and print them on a paper would pass the counterfeit-check. As long as the server gets the same scanned photo, regardless of the source (genuine sticker or copied sticker), it will pass the check.

RFID and NFC are no different than holograms when it comes to copying them. It is even easier, all you need is the RFID/NFC code set in one of the original item and set the same code in cloned RFID/NFC labels/tags, and you will be ready to pass the counterfeit check! Usual cost varies from few cents to a dollar based on type of RFID (active/passive) or NFC tags.

Companies, who provide the unique code per product, make more sense. There are two type of Codes usually provided:
If the codes are open (not protected by some scratchable layer), then it is of not much use, anyone can copy them and pass the counterfeit check, no matter what company claims about the crypto tech, block-chain or advanced technology they use in the backend (although with the help of geo-location tech and AI, red flags can be raised for some cases).
Truth is, if you have the same code as the original, which you can see without buying the product, then you can copy it, put it on counterfeited product and pass the counterfeit-check.
Also, in the market, many say putting the supply-chain data on block-chain prevents counterfeiting - it is definitely not-true. Printing the code on the item means you are making the key to access the data on block-chain public, now any one can copy and replicate this code and pass the check. Block-chains are meant for totally different purpose and have different use-cases, and preventing the counterfeit of general goods is not really one of them.
Please note - by block-chain, we mean the block-chain in terms of technology, we have encountered many non-technology and business development people who confuse block-chain technology to something totally different depending on the context. To learn what really is a block-chain and how it can be made fast and cost effective, to be utilized for business-cases, you can check our whitepaper fast private blockchain
These are the physically protected QR or Barcode or Alphanumeric codes and you must buy the item before you can see the code, for example, scratchable card, and then verify with the backend server.
This does protect the item and if the backend technology is
implemented properly, i.e. non-guessable codes are generated, then
this will prevent the counterfeit.
But problem is, user has no idea before buying the item if it will
be genuine or not, not only this company who has not implemented the
backend properly may pass some items which may be fake, or may pass
already scratched code again and again.
Secondly, if their DB is hacked then it will be very simple for the
hackers to sell the codes to Counterfeiters.
The development and more importantly maintenance and security of
such system is not simple and usually costs good maintenance cost.
And the authenticating servers will have to be always online.
Introduction of NeuroTags Technology
Finally to provide better anti-counterfeit protection, we designed and implemented NeuroTags technology.
We kept mainly 3 things in mind:
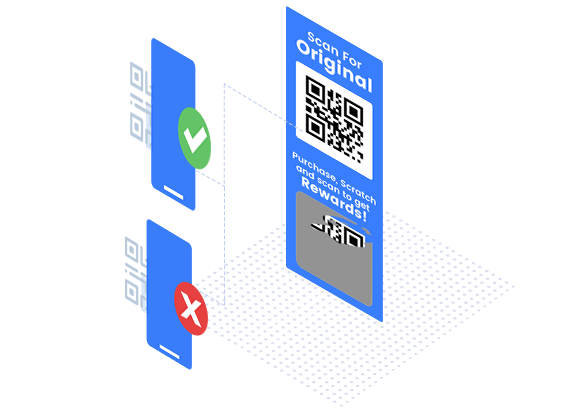
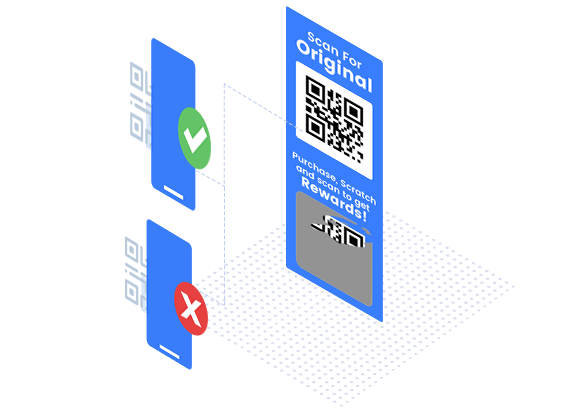
This is the most difficult part to design. After careful thoughts, we have introduced two tags which go together, one open (pre-purchase) tag and one protected (post-purchase) tag and each of them is unique for each product.
User can scan the pre-purchase tag before buying and get a good estimation of genuineness of the product and check any RED flags. And scanning the post-purchase tag (which is accessible only after purchase of the item) provides complete genuineness information.
There are two protection we have given to pre-purchase tag:
Protection to post-purchase tag:
Security of the auth system and tags are the most important criteria in designing the system.
Having the team with experienced ethical hacker, experience fighting hackers in gaming companies in past (Gala Net) and designing the secure systems for finance companies (Paypal) has helped not to overlook any potential cases where security can be a problem.
We can not expose more here, but our tags info is one way "scrypt" and private key secured so even if someone gets the DB of tags he or she can not get the tags code.
We have made sure the NeuroTags can be scanned without need of any app download. This removes any friction from user's side.
User can manage the purchases, warranty of the products and access to customer support with just a single scan.
Codes can be scanned by any scanner app, for iOS and new Android phones native camera works,
also scanner of the popular apps, such as, WeChat, can be used.
The technology is cost effective, on the cloud and efficient to use so that it can be used by any company of any scale, without worrying about the cost. In most of the cases, the overall cost of our technology is usually lower than putting a hologram.


Overall Value Summary
A technology is useless if it can not be effectively put into use for mass adoption. While designing the NeuroTags technology we have made sure it has short and long term business benefits.